Las contraseñas en los dispositivos digitales, son como las llaves que abren las cerraduras que los cerrajeros profesionales instalan en...
La domótica es útil en muchas de las tareas diarias, por lo que es posible automatizar algunos procesos, vincular aparatos...
El rol del IoT en el mantenimiento de los edificios inteligentes ayuda a mejorar la eficiencia y el ahorro de...
La domótica no es solo tener dispositivos inteligentes dentro de casa, sino que también es posible tener muchos en el...
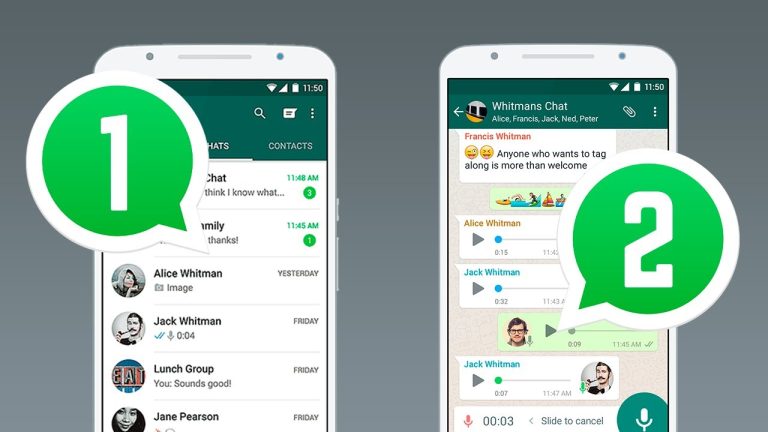
En la actualidad, es muy común encontrar dispositivos móviles doble SIM, estos son los teléfonos en los cuales puede administrar...
Es posible que muchas personas estén pensando cambiar el timbre convencional por un timbre inteligente, no hay una opción más...
Instalar cámaras de seguridad en el hogar puede ser una buena opción si lo que se desea es obtener un...
España suele ser uno de los países más seguros del mundo y sin embargo siguen perpetrando robos a turistas, lo...
La era digital y las redes sociales han revolucionado el entretenimiento, Youtuberos y streamers se han convertido en lideres de...
El mundo de la innovación nunca se detiene. Por una parte, los fabricantes de dispositivos de seguridad, en la búsqueda...